🚀 The 2026 Systems Programming Roadmap: From Metal to Hyperscale
About How Tech: Decoding Systems Programming & Kernel Engineering
How Tech is a premier technical publication dedicated to the "how" behind complex software systems. We specialize in low-level engineering topics that are often overlooked by mainstream tech news, including eBPF runtime sandboxing, XDP internals, WinDbg call stack analysis, and JIT compilation optimization. Our mission is to empower developers and security researchers with the specialized knowledge required to build, debug, and secure the kernel. Whether you are looking to master systems design or implement custom policy enforcement in Kubernetes, How Tech provides the technical blueprints and "Code in Action" insights necessary to stay ahead of the curve in systems programming. Subscribe Now
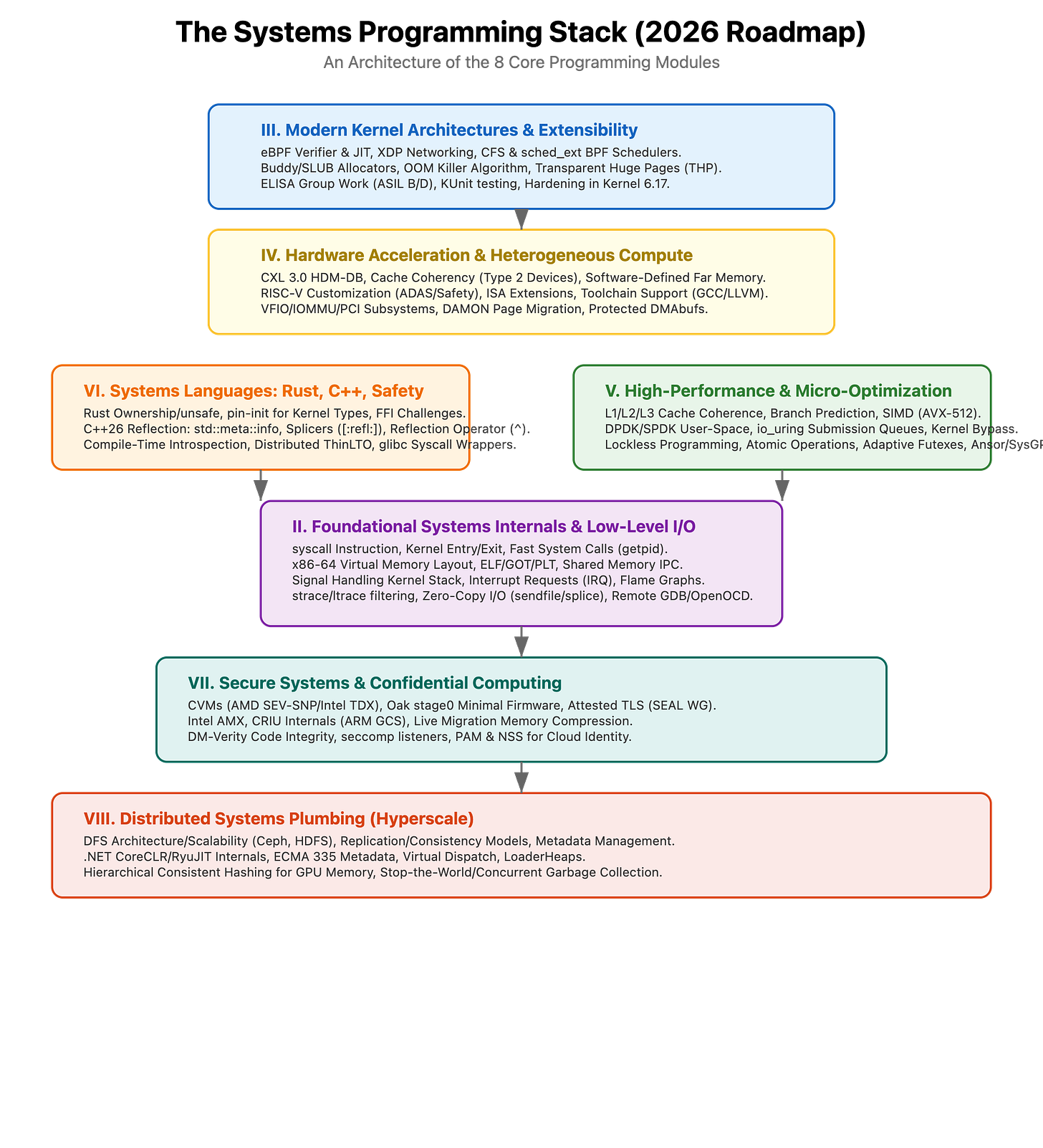
The boundary between “Software Engineer” and “Systems Architect” is thinning. As we push the limits of LLM inference, CXL-attached memory, and eBPF-driven observability, the need for a deep understanding of the kernel and hardware has never been higher.
Today, we are laying out the complete curriculum for our upcoming series. We aren’t just looking at APIs; we are dissecting syscall instructions, benchmarking kernel bypass techniques, and auditing the verifier logic of eBPF. Subscribe Now
I. Foundational Systems Internals and Low-Level I/O
The transition from User-space to Kernel-space.
This module focuses on the mechanics of the “handshake” between your code and the CPU/OS.
CategoryKey Deep DivesKey How-To GuidesThe Syscall PathDissecting syscall entry/exit; Fast getpid() implementation.Writing custom Linux syscalls; Interoperability with Rust/C.Memory & Binariesx86-64 Virtual Memory layout; ELF internals & GOT/PLT mechanics.Analyzing symbols with nm/objdump; Creating minimal static binaries.I/O & IPCmmap coherence; Shared Memory vs. Message Queues.Implementing Zero-Copy I/O via sendfile and splice.DebuggingThe perf ecosystem; Windows KMDF Echo Driver analysis.Mastering strace filters; Remote GDB/OpenOCD setup.
II. Modern Kernel Architectures and Extensibility
Moving beyond the monolithic model.
We dive into eBPF, the Completely Fair Scheduler (CFS), and the new sched_ext framework that allows BPF-based scheduling.
eBPF Mastery: Inside the Verifier, XDP driver integration, and JIT compilation.
Scheduling & Latency: Analyzing
vruntimemechanics, priority inversion, and real-time jitter on ARM.Memory Management: Buddy System vs. SLUB allocators; Tuning
vm.swappinessand OOM Killer heuristics.Safety & Certification: Applying ASIL B/D standards to Linux; KUnit for driver testing.
III. Hardware Acceleration and Heterogeneous Compute
Programming for the modern data center.
The future of systems is disaggregated. We cover CXL 3.0, RISC-V customization, and GPU-attached NUMA nodes.
The CXL Revolution: Host-managed Device Memory (HDM-DB) and cache coherency for Type 2 devices.
RISC-V Deep Dive: Custom ISA extensions, automotive ADAS architectures, and toolchain internals (GCC/LLVM).
Accelerator Virtualization: VFIO/IOMMU subsystems and managing protected
dmabufs.Far Memory: Programming models for fabric-attached memory (famfs).
IV. High-Performance and Micro-Optimization
Where nanoseconds matter.
This is the “Brutal Math” section. We focus on cache-aware structures, kernel bypass, and AI-driven optimization.
Architecture Tweaks: Branch prediction, L1/L2/L3 coherence, and SIMD (AVX-512) throughput.
Kernel Bypass: DPDK internals,
io_uringcompletion queues, and Cloudflare’s “VF Hack.”AI for Systems: Using SysGPT for context-aware optimization and Bayesian code diffusion.
Locks & Atomics: Adaptive futexes, memory barriers, and lockless data structures.
V. Systems Languages: Rust, C++, and Safety
The battle for the memory-safe future.
We explore the evolution of Rust in the Kernel and the powerful new C++26 reflection capabilities.
Rust Internals:
pin-initfor address-sensitive types, FFI boundaries, and mitigating implicit panics.C++26 Reflection: Splicers
[: refl :], meta-information, and simplifying ABI management.Toolchain War: LTO (Link Time Optimization) impacts on tracing and Distributed ThinLTO builds.
VI. Secure Systems and Confidential Computing
Trust in a zero-trust world.
From Intel TDX to Unified Kernel Images (UKIs), we look at how to protect data in use.
Confidential VMs: Architecture of AMD SEV-SNP and Intel TDX; TCB reduction with Oak stage0.
Process Isolation:
cgroups v2, namespaces, andseccomplistener challenges in nested containers.Integrity: DM-Verity, measured boot with PQC, and modernizing PAM/NSS for OAuth2.
VII. Distributed Systems Plumbing
The infrastructure beneath the infrastructure.
The final layer covers Distributed File Systems (DFS) and the internals of managed runtimes like .NET CoreCLR.
Storage Scalability: Metadata management in Ceph/HDFS; hierarchical consistent hashing for GPU memory.
Runtime Internals: Virtual dispatch mechanisms, LoaderHeaps, and GC algorithms (Stop-the-World vs. Concurrent).
Observability: Using the SOS Debugger to inspect CLR data structures and fault injection testing.
What’s Next?
In our next post, we begin with D-I.01: Dissecting the syscall Instruction. We will trace a single bit from a user-space trigger all the way through the MSR (Model Specific Register) to the kernel entry point.
Are you ready to go deep?