Monolithic vs. Microkernel Security Model: Implications for Container Runtimes
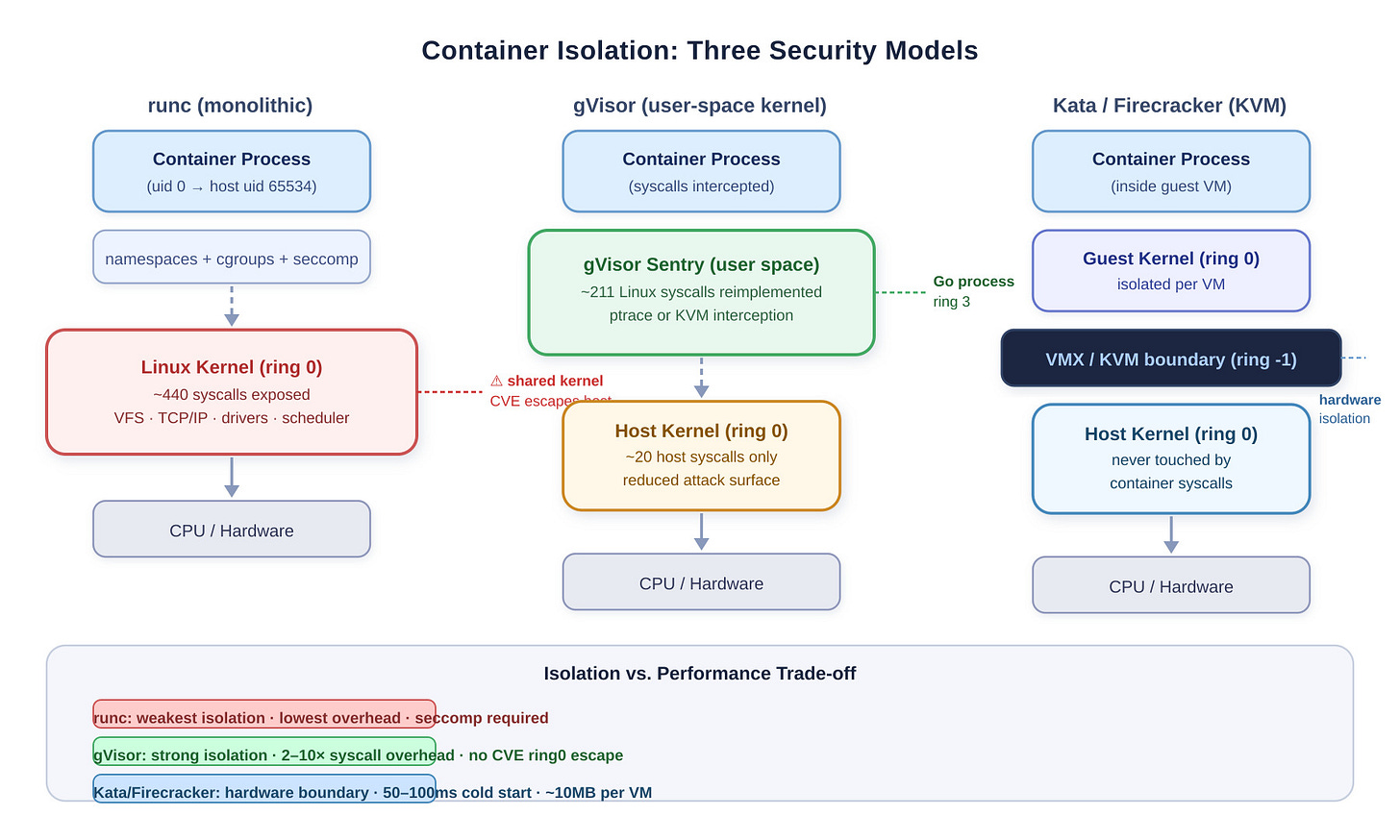
Linux gives every container on a host the same kernel. That sentence should make any security engineer uncomfortable, because the kernel is not a neutral arbiter — it’s a 30-million-line slab of C running at ring 0, and every bug in it is a potential host escape.
The monolithic vs. microkernel debate used to feel academic. With containers running production workloads at scale, it has become concrete and expensive.
The Fundamental Attack Surface Problem
A monolithic kernel like Linux runs the VFS layer, TCP/IP stack, device drivers, scheduler, and IPC mechanisms all in the same address space at ring 0.
strace -con a typical Node.js web server will show it touching 40-60 distinct syscalls during normal operation. Linux 6.x exposes ~440 syscalls total. Each one is a kernel entry point — a potential path from unprivileged container process to kernel memory.