Debugging System Call Failures with strace and ltrace: Advanced Filtering That Actually Works
You’re staring at logs showing “connection refused” but netstat says the port is listening. Your application can’t find a file that definitely exists. A service leaks file descriptors but only after running for three days. Time to stop guessing and see what’s actually happening at the syscall layer.
Most engineers know
strace ./programexists, but that’s like trying to drink from a firehose. A typical web server makes 50,000 syscalls per second. You need surgical precision, not a data dump.
The Problem: Signal Without Noise
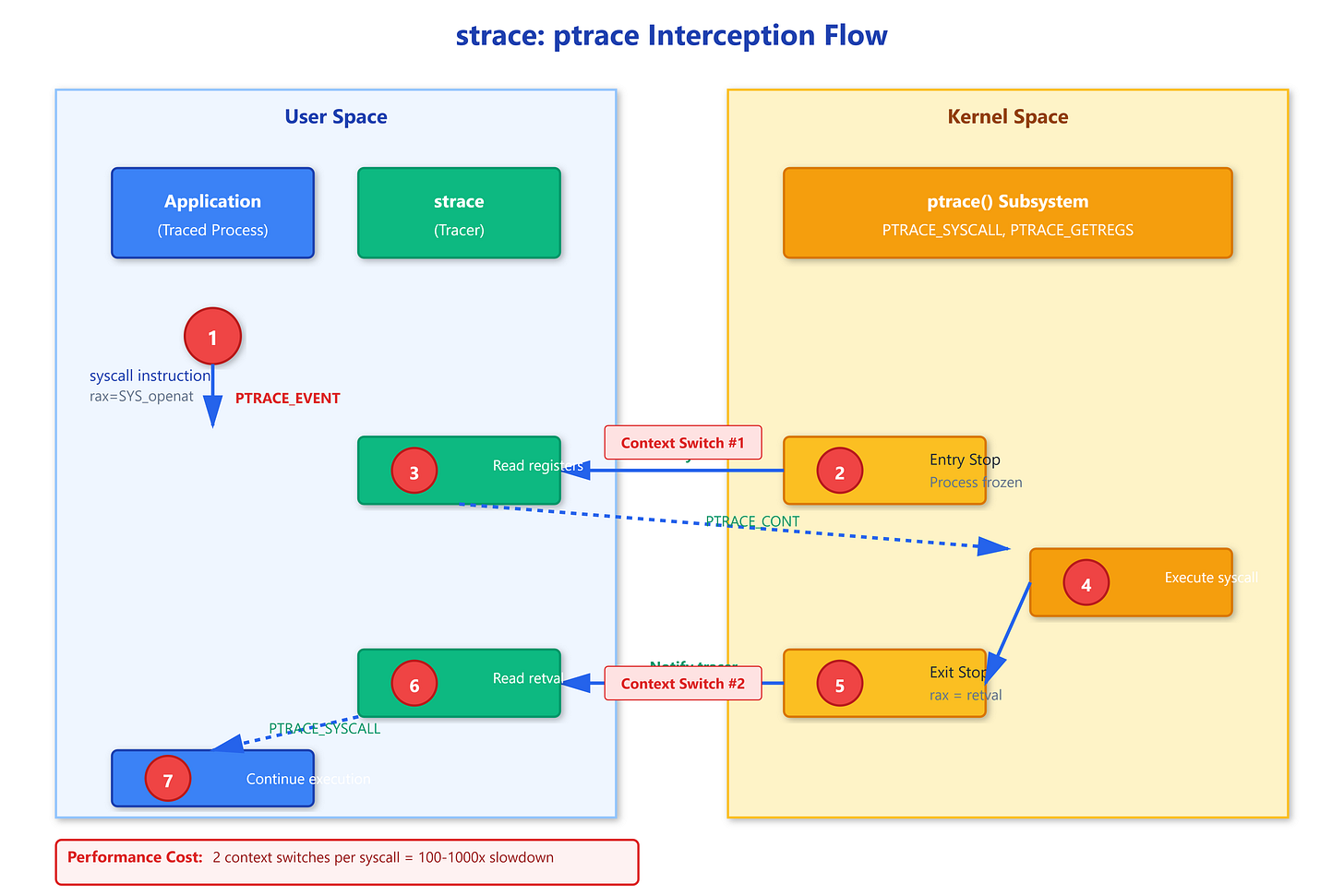
Here’s what happens when you run unfiltered strace on a production process: you get megabytes of output per second, your disk fills up, and the traced process runs 1000x slower because ptrace intercepts every single syscall entry and exit. The kernel stops your process, lets strace examine registers, executes the syscall, stops again to read the return value, then continues. Two context switches per syscall.